envpass
Encrypted secret sharing for hackathon teams.
Overview
Every hackathon team hits the same moment — someone sets up the Stripe sandbox and the OpenAI key and now needs to get those credentials to three other teammates. What follows is API keys dumped raw in Discord DMs, .env screenshots in group chats, and secrets sitting in plaintext in places they shouldn't be.
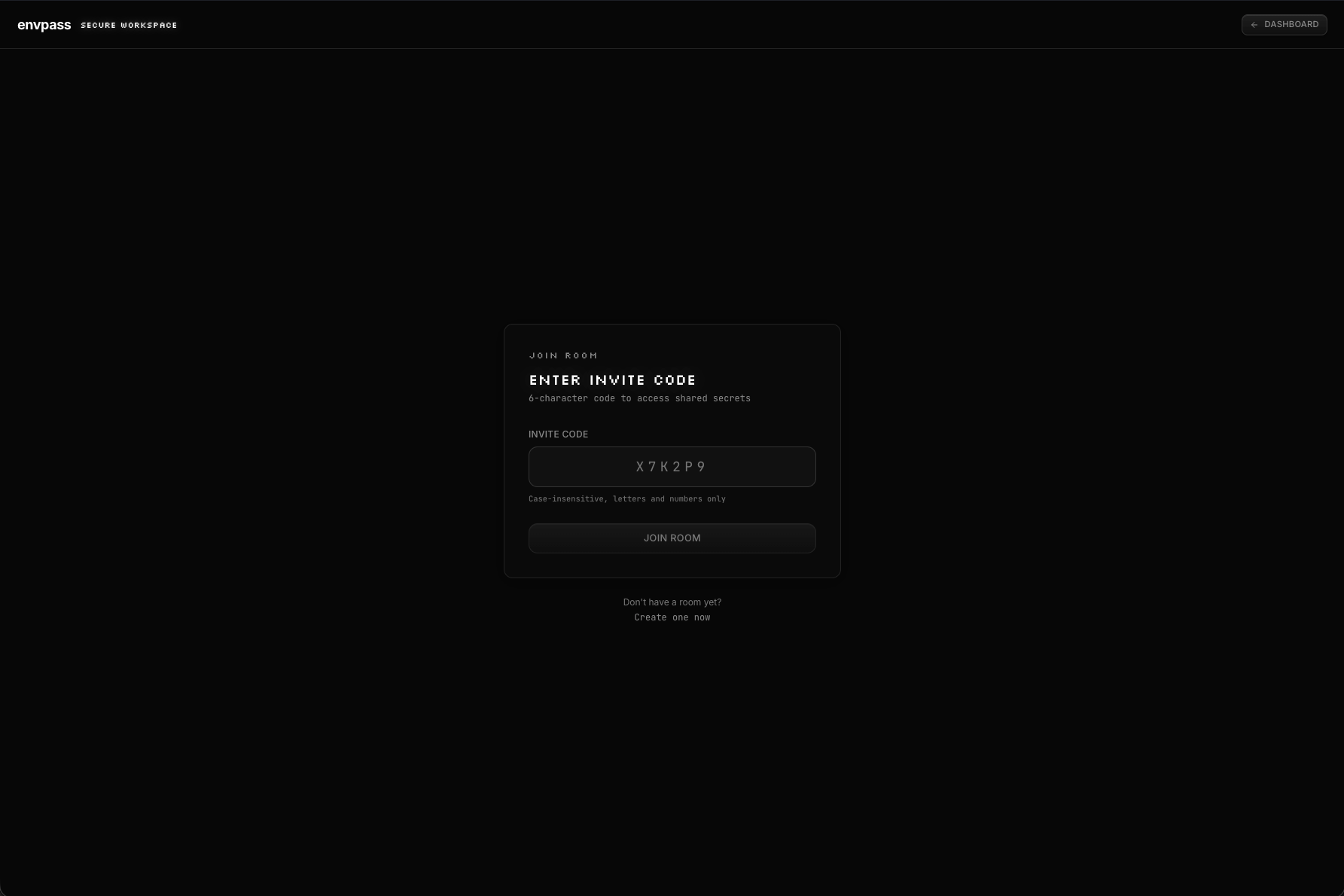
envpass replaces that entire workflow with a secure, real-time vault. Create a room, get a 6-character invite code, and your team has an encrypted space to share secrets — synced instantly via Convex, encrypted at rest via WorkOS Vault, and shredded when the hackathon's over.
The Problem
Sharing API keys and environment variables during hackathons is a security nightmare. Teams routinely paste secrets in plaintext across Discord DMs, Slack channels, emails, and shared docs. These credentials persist indefinitely in chat histories and can be compromised if any of those channels are breached.
Existing solutions like Doppler, 1Password, and HashiCorp Vault are built for enterprise teams with onboarding friction that doesn't fit the pace of a 36-hour hackathon. There's no tool designed specifically for fast, ephemeral, secure secret sharing at hackathon speed.
The Solution
envpass is a web app purpose-built for the hackathon use case. A room owner creates a vault, gets a short invite code they can share verbally or via text, and teammates join to access encrypted secrets in real-time.
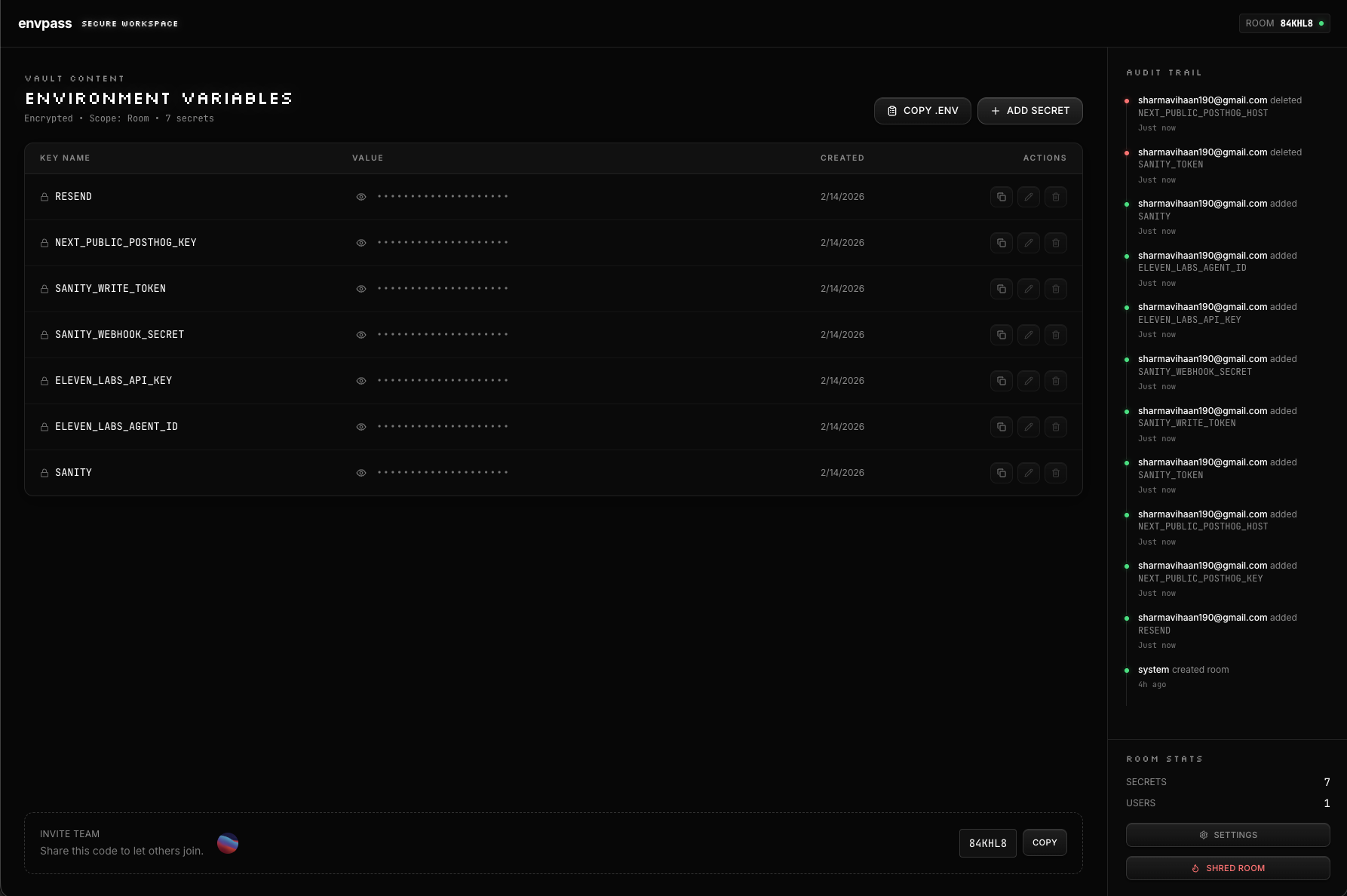
Every secret value is encrypted via WorkOS Vault using HSM-backed envelope encryption with a unique data encryption key per secret. The Convex database only stores opaque Vault object references — never plaintext. Values are masked by default in the UI and decrypted on-demand only when a user copies to clipboard, which auto-clears after 30 seconds. A full audit trail logs every read, write, copy, and export with the user and timestamp.
Key Features
HSM-Backed Encryption
Every secret is encrypted with a unique key via WorkOS Vault's envelope encryption. The database stores only opaque references — plaintext values never touch our infrastructure.
Real-Time Sync
Powered by Convex's reactive subscriptions. When a teammate adds a secret, it appears in everyone's room instantly — no polling, no refreshing.
Bulk .env Import & Export
Paste an entire .env file and envpass parses and encrypts each key-value pair individually. Export everything back out as a downloadable .env file with one click.
Copy-Only Access
Secret values are masked by default. Users copy to clipboard on-demand — the decrypted value is never rendered in the DOM. Clipboard auto-clears after 30 seconds to prevent lingering exposure.
Full Audit Trail
Every secret read, write, copy, export, and member change is logged with the user and timestamp. Room owners have complete visibility into who accessed what and when.
Room Shredding
When the hackathon's over, the room owner shreds the room — deleting all secrets and membership data. No lingering credentials.
Results & Impact
Built in One Day
Went from idea to deployed product in a single day, demonstrating that secure infrastructure doesn't require weeks of setup when leveraging the right tools (WorkOS Vault + Convex + Next.js).
Zero Plaintext Architecture
Successfully implemented a system where the application database never stores a single plaintext secret value — only opaque encrypted references that are useless without access to WorkOS Vault's HSM-backed keys.
Open Source
Fully open-sourced on GitHub, allowing anyone to audit the security model, verify the encryption claims, and self-host if desired. Transparency as a trust mechanism.